Get A ... Get B ... Release A ... Release B
Get B ... Get A ... Release B ... Release A


- Processors,
- I/O channels,
- main and secondary memory,
- devices
- data structures such as files, databases, and semaphores
- Deadlock occurs if each process holds one resource and requests the other
- Example: 2 processes each need 200K. There is 250K available. If each grabs 100K, and then they try to grab the remaining... deadlock.
- Interrupts,
- signals,
- messages,
- information in I/O buffers
- Example, 2 processes do a receive before doing a send.

- Mutual exclusion - Only one (or at least a finite number)process may use a resource at a time
- Hold-and-wait - A process may hold allocated resources while awaiting assignment of others
- Preemption - No resource can be forcibly removed form a process holding it
- Actual deadlock also requires circular wait.
- Prevent
- Avoid
- Detect
- Not much we can do about mutual exclusion
- Hold and Wait - require process to request all resources at once.
- Preemption - processes can lose resource and must re-request.
- Circular wait - set order or resource requests.
- A process is only started if the maximum claim of all current processes plus those of the new process can be met. Not optimal
- Banker's Algorithm.

- Safe state is where there is SOME order to run all processes
to completion.
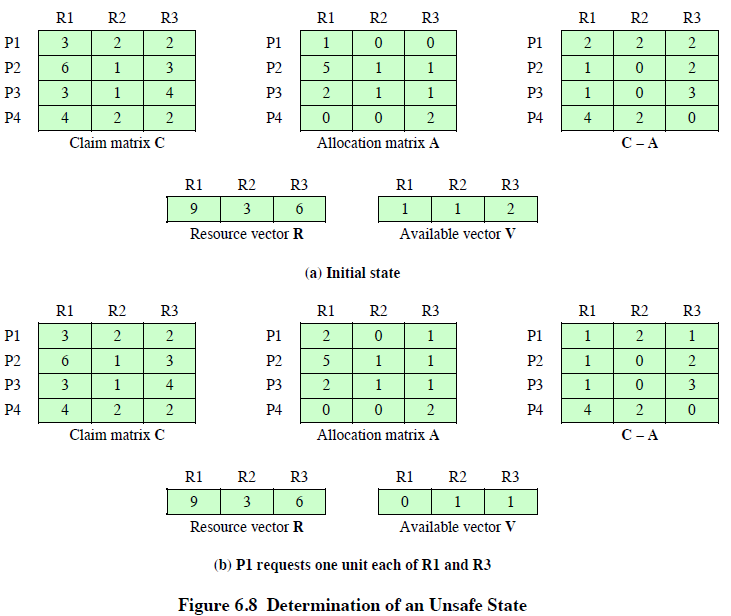
- When a process makes a request for a set of resources, assume that the request is granted, Update the system state accordingly, Then determine if the result is a safe state. If so, grant the request and, if not, block the process until it is safe to grant the request.
- Less restrictive than prevention.
- Detect and break deadlock.
Mark all processes that have been allocate 0 resources.
\( W = V \)
Find process i s.t. \( Q_i \leq W \)
\(W = W + A_i\)
repeat until no i, or all processes are marked.
- Any process unmarked is deadlocked.
- Abort all deadlocked processes
- Back up each deadlocked process to some previously defined checkpoint, and restart all process (Risk of deadlock recurring)
- Successively abort deadlocked processes until deadlock no longer exists
- Successively preempt resources until deadlock no longer exists
- Deadlock
- Odd grabs left, even grabs right.
- Room semaphore.
- Pipes
- msgsnd and msgrcv
- Semaphores
- Atomic ops:
- atomic_read(atomic_t *v)
- atomic_set(atomic_t *v,int i)
- atomic_add(int i,atomic_t *v) ...
- atomic_dec_and_test(atomic_t *v)...
- spinlocks
- reader-writer semaphores