- We're already spoken about access control in linux, but what other systems are there?
- In the unix-style access control, one weakness is that if one
person has access to a reseource, they might be able to allow others to access that resource.
- "Mandatory Access Control (MAC)
refers to a type of access control by which the operating system
constrains the ability of a subject or initiator to access or
generally perform some sort of operation on an object or target. In
practice, a subject is usually a process or thread; objects are
constructs such as files, directories, TCP/UDP ports, shared memory
segments, IO devices etc." - Wikipedia
- The key is that there is a central security policy administrator that makes decisions, and individual users cannot alther rights.
- This makes systems nearly unusable in a shared development
environment, but you can certainly see in a deployed users-only
environment, this would afford extra protections. Military systems with classified data typically use some sort of sinilar nechanism.
- Currently, formas of MAC exist in SELinux, and is an extra layer in Ubuntu (AppArmor) and Windows.
- RBAC
- Users are mapped to ROLES, which are mapped to then to resources.
- This makes sense in a corporate environment where people change
jobs, or their jobs change responsibilities frequently. When a new
person moves into a role, just that fact be noted, not update all
the the individual permissions.
- Intrusion detection.
- If our security fails in some way, it would be great to know.
- If we find out soon enough, we can eject the attacker before any
damages is done.
- We can observe the attacker to try and trace he source.
- We can figure out how he got in to strengthen our defenses.
- Setting one up is an art. False negatives mean we missed an attacker (which is bad) yet false positives mean we flag a valid user, which is also bad.
- Intrusion Detection can be done on the network, or on the host.
Since this is OS, we're looking at the host.
- Monitor the system to detect suspicious bahovior. 2 Approaches:
- Anomally detection: apply statistical tests to behavior to see
if it conforms to historical norms. Can either look at a global
threshold, or have a model for each indivivual account profile.
- Not as useful against internal threats.
- Signature detection: store patterns of known attacks.
- Audits.
- Native. Most systems log activity, but this might not be in
a useful format. Gravelling through lots a extra data slow.
- Detection specific - generate audits of information that is
especially useful. We try do break a single command into
substeps, and record: subject, action, object, exceptions,
resources used and time stamp.
- So a copy command has an execute step, a read step and a
write step.
- This way we can easily break down activity by type OR OBJECT.
- Malware defense.
- Anti-virus. Don't let a virus get on the system. if it does,
detect, identify and remove.
- Signature detection. The basic model for detection is to
keep a database of unique identifiers of all known viruses,
and scan for those byte sequences. Unfortunately, virus makes
were long ago on the that scheme, so they began to encrypt the
virus as it was installed in an executable.
- Generic Decryption. Whne a process is to be run, run it
in simulation first, let the virus decrypt itself, and then
comepare to db. slow. Slow. SLOW!!!
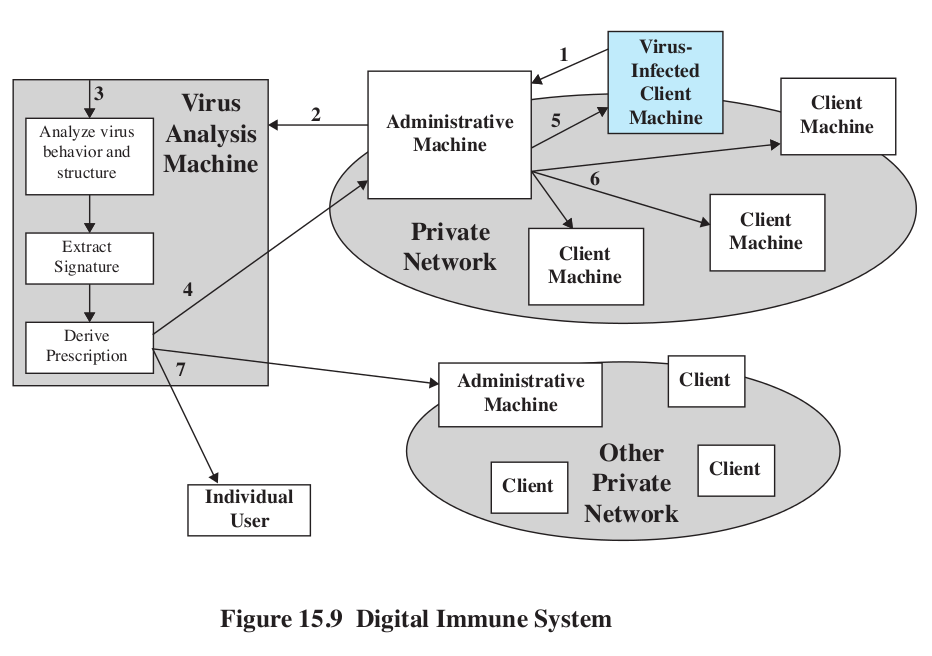
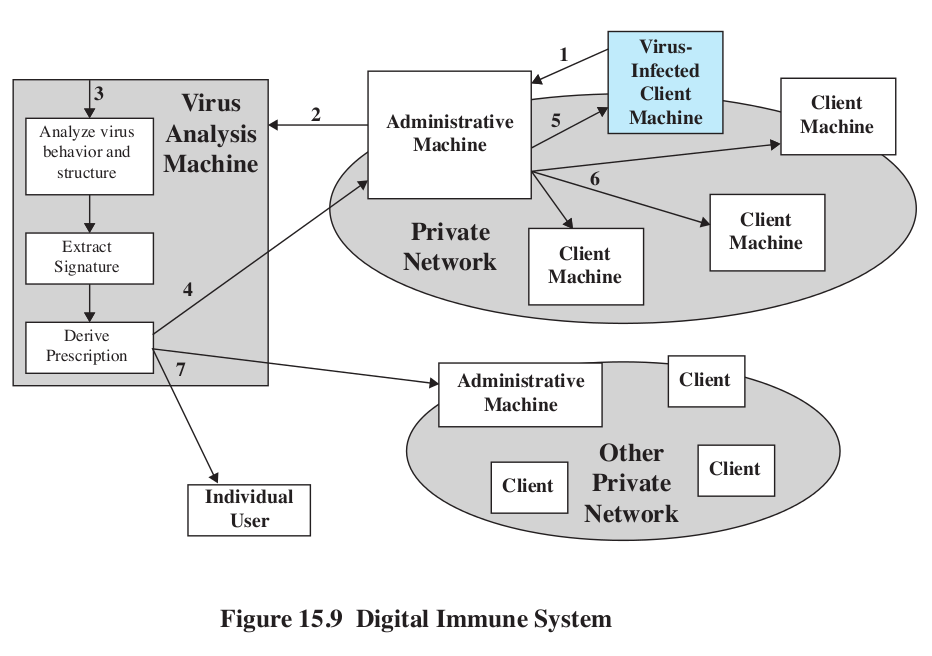
- Digital immune system (Symmantec)
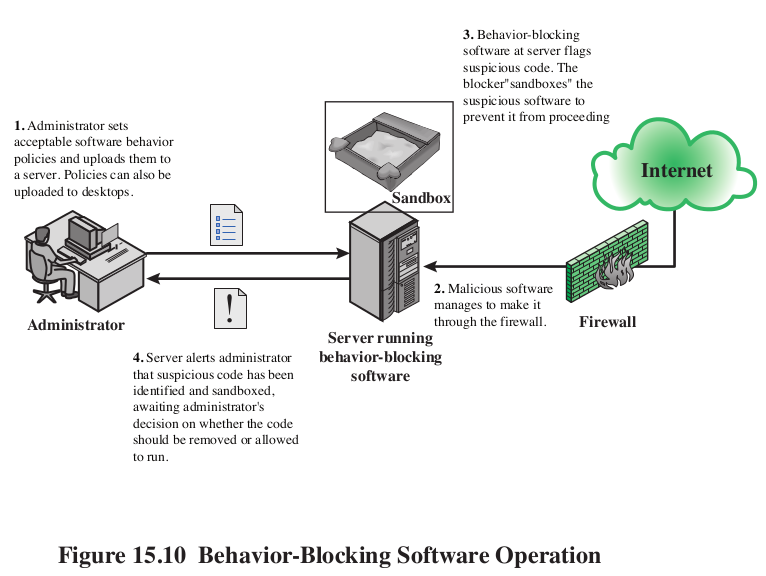
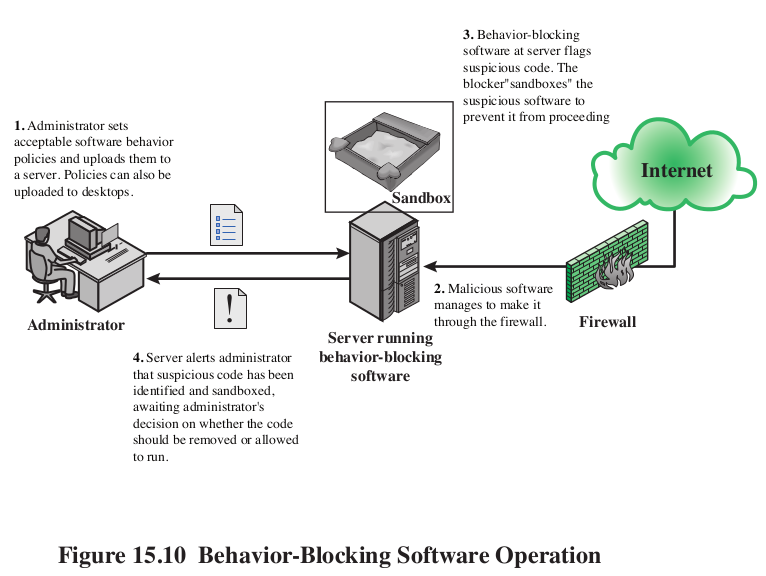
- Behavior blocking. Just don't let programs perform certain
actions, like modifying other programs. Of course, then some
things become hard. Sandbox the offender until administrator
can take a look.
- Worm countermeasures. Very similar to virus.
- Signature of scan patterns.
- Signatures in incomming packets.
- Payload classification.
- Looking for randomness in scans.
- limiting outbound traffic from hosts that scan too much.
- Shutting donw network for hosts that scan too much.
- Rootkit countermeasures.
- Once a rootkit is successfull, badguy can erase traces of rootkit.
- Signatures can work, if you scan at the right time.
- Look for interference in system calls.
- Scan hashes of files to saved hashes to see if they've
been modified.
- Only secure response is complete reinstall from scratch.